User Tools
Sidebar
This is an old revision of the document!
Table of Contents
VIM3/3L Secureboot

save temporary
Introduction
The default firmware compiled by Fenix for Ubuntu/Debian does not support Secureboot. For ordinary users, Secureboot functionality is not necessary. Enabling Secureboot means that the board can only flash firmware signed with the same key. It won't be possible to flash any other unsigned firmware or firmware signed with a different key. Additionally, the process of flashing the key is irreversible.
If you need to add Secureboot support, you will require additional patches to enable it.
Apply patches to support secureboot
Download and apply patches .
~/vim3-secureboot-patches$ tree
.
├── fenix
│ └── 0001-packages-images_upgrade-bump-to-1b40968.patch
└── u-boot
└── 0001-don-t-decrypt-dtb-when-secureboot-enabled.patch
2 directories, 2 files
There 2 patches, one is for Fenix, and the other one is for u-boot.
Compile the images
You can compile the images after apply the patches.
Generate the signing key
Download the sign tool decompress it and double click AmlEToolV3.exe to open it:
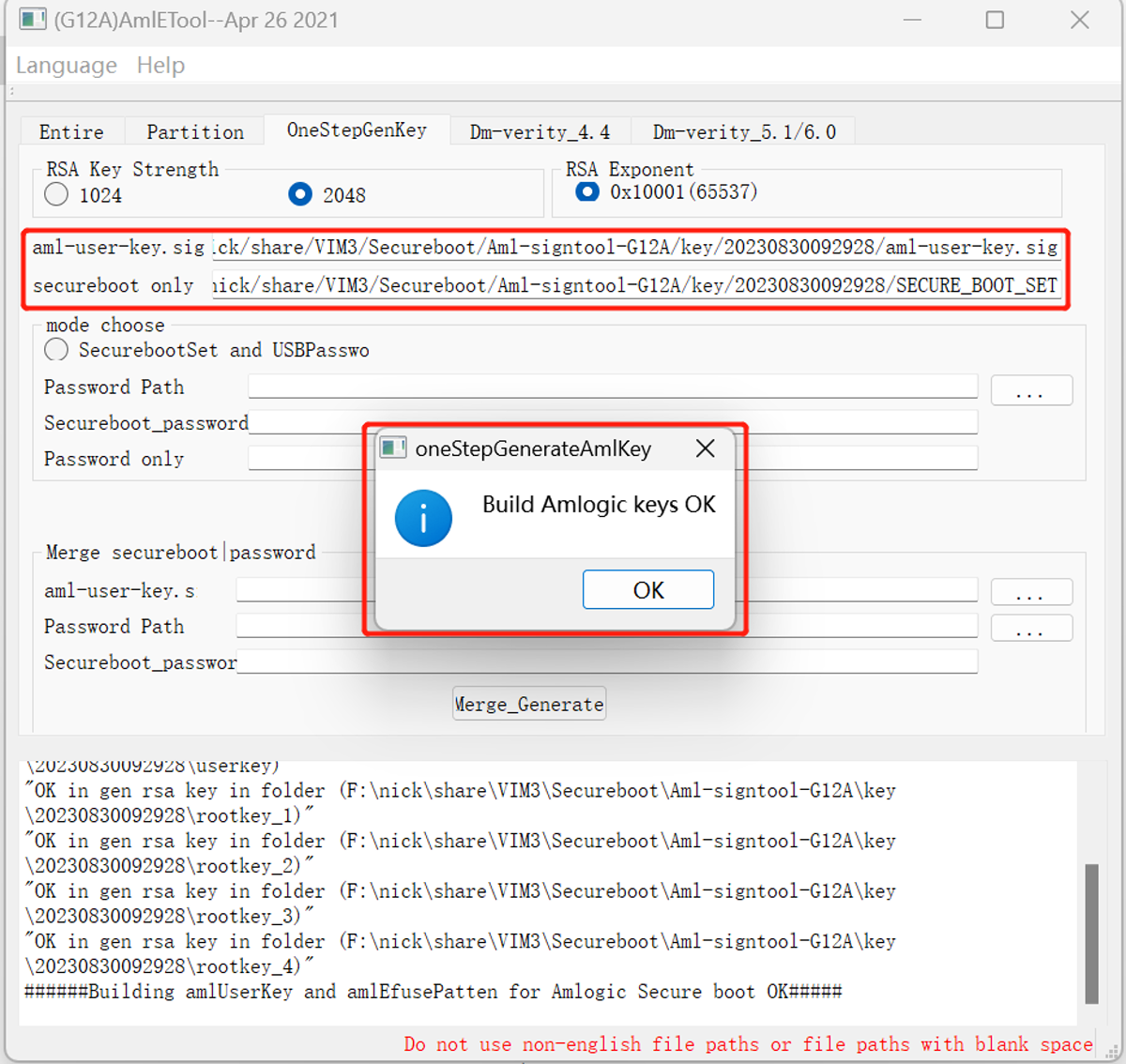
Select OneStepGenKey and check 2048 then click Generate to generate the keys:
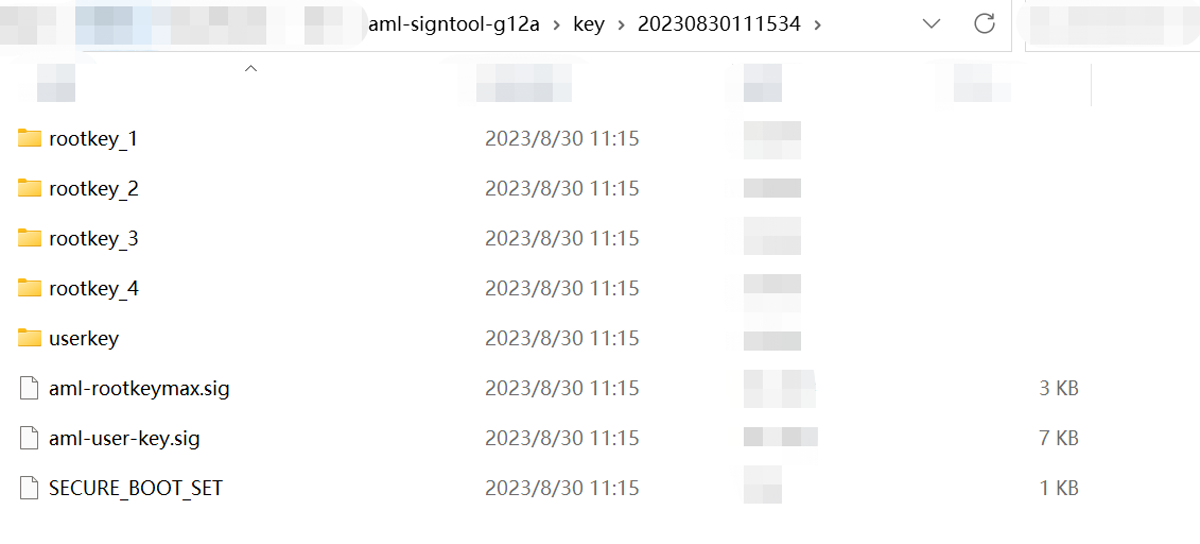
The path of generated keys is in the key directory within the current sign tool's directory, named after the current time, e.g.
You need to save the files aml-user-key.sig and SECURE_BOOT_SET:
- aml-user-key.sig - Used to sign the images - SECURE_BOOT_SET - Used to burn the key
Encrypt the images
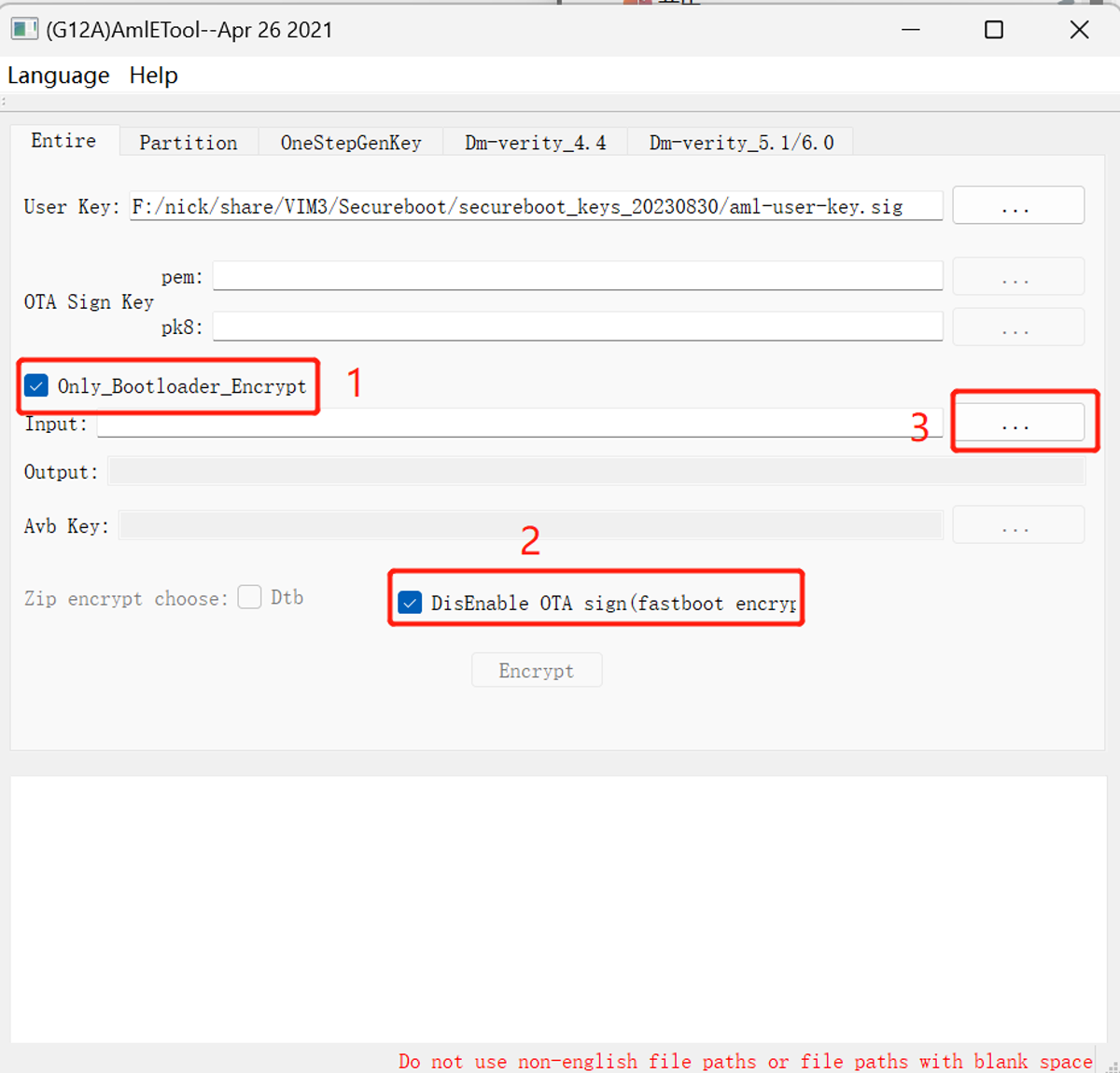
Still using the sign tool AmlEToolV3.exe, select Entire, import the User Key, which is the file aml-user-key.sig generated before,
and also check Only_BootLoader_Encrypt and Disable OTA sign. Then, import the image that needs to be encrypted in the Input:
Then click Encrypt to encrypt the image.
After successful signing, a new encrypted image will be generated in the original image directory, with a filename containing the secureboot suffix,
e.g. if the orignal file is vim3-ubuntu-22.04-server-linux-4.9-fenix-1.5.2-230830-emmc-develop.img, then the encrypted image is vim3-ubuntu-22.04-server-linux-4.9-fenix-1.5.2-230830-emmc-develop.20230830105011.secureboot.img
Next, we will explain how to flash this encrypted image.
Flash encrypted image
Download and install the [[dl>products/vim3/tool/usb_burning_tool_v2.2.0.zip | USB flash tool), after installation, you need to copy the previously generated file
SECURE_BOOT_SET to the licence directory within the USB tool installation directory,e.g. C:\Program Files (x86)\Amlogic\USB_Burning_Tool\license.
Open the USB flashing tool, import the encrypted image, check the secure_boot_set option, and then click Start to start the flashing process.
The key can only be flashed once, meaning you should only check secure_boot_set during the first encryption firmware flash.
Do not check it again for subsequent flashes or it will fail.
Warning
- The Secureboot key can only be flashed once, and it is irreversible, so caution is advised when flashing. - The generated key must be securely stored because once the key is flashed, you will only be able to flash images signed with this key in the future. - Make sure to conduct thorough testing and ensure that the image is production-ready before enabling the Secureboot feature.